Connected vehicles may be subject to all the cyber types of attacks that IT networks and endpoints suffer, now and going forward. Since connected vehicles store valuable driver and consumer data, we can expect these nuggets of personally identifying information to be prized targets.
To guard against such attacks, security teams must deploy Intrusion Prevention and Detection Systems and Vehicle Security Operation Centers (VSOCs) staffed 24/7 with security analysts from Tier 1 to Tier 4 for vehicle hacking protection. VSOCs keep vehicles and their operational databases secure just like SOCs keep organizational networks secure. VSOCs collect and monitor data from vehicle fleets raising alarms when there is a detected threat and forecasting the probability of failure for each vehicle component.
The industry will cooperate on timely threat intelligence to keep all OEMs and suppliers up to date concerning threats, their identification and appropriate response. We can expect a concentration of organized syndicates to target vehicles specifically because the cyber-stakes are so high.
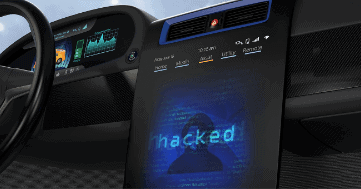
The attack vector of choice will have vehicle ransomware as its ultimate goal, the ability to force drivers, owners, fleet operators, manufacturers and others to pay a ransom to continue to use their automobiles. Over 50% of enterprises were hit by IT-related ransomware last year costing businesses 20 billion dollars.
We can expect such numbers to carry over to the 381 million connected vehicles on the road today. While the current rate of ransomware payout in the IT world is $500 per endpoint per incident, the figures will be much higher for cars and still higher for trucks. Large fleets will be hit up for millions of dollars (preferably paid in cryptocurrency) to get their cars and trucks back into operation. Elon Musk, founder and CEO of Tesla has stated, “I think one of the biggest risks for autonomous vehicles is somebody achieving a fleet-wide hack.” It is not just the newer connected systems which are vulnerable to interference either, as even the standard and long-time serving components can be a target for attack as proven with CAN bus hacking demonstrations.
“I think one of the biggest risks for autonomous vehicles is somebody achieving a fleet-wide hack.”
Elon Musk, founder and CEO of Tesla
Because the stakes are so high, ransomware attacks on cars and other vehicles attract the elite among hackers. In fact, we will see nation-state actors get involved in this “lucrative” practice making the job of defense tougher than ever and enforcement of international laws and regulations extremely difficult. Nobody blames Dell or Asus for a ransomware attack that strikes their laptops in a given enterprise. However, in the case of vehicles, the damage to the reputation of a car manufacturer could be astronomical as consumers shun their products for more cyber-secure models. Therefore, we must be wary of players at all levels in the automotive supply chain trying to gain a competitive advantage by delivering a payload of ransomware or other type of attack against a rival’s products.